Understand your cyber risk in dollars and cents with Resilience's free Cyber Risk Calculator
Data breaches cost U.S. businesses an average of $9.36 million per breach in 2024, yet many enterprises still struggle to quantify their specific cyber risk exposure in financial terms. How do you translate complex technical vulnerabilities into language that your CFO, board members, and other stakeholders can understand and act upon?
We’re excited to announce the launch of Resilience’s free Cyber Risk Calculator – a powerful tool designed specifically for medium-to-large enterprises to quantify their cyber risk exposure in clear dollar terms.
Bringing financial clarity to cyber risk
For too long, cybersecurity and financial risk have spoken different languages: Security teams talk about vulnerabilities and threats, while financial leaders focus on dollars and cents. This fundamental disconnect creates significant challenges across the organization, particularly when trying to align priorities and allocate resources effectively.
Quantifying cyber risk in financial terms has been notoriously difficult, leaving many organizations struggling to communicate potential impacts to non-technical stakeholders. Without this shared understanding, companies often find themselves making security investment decisions based on incomplete information or industry trends, rather than their specific risk profile.
Our Cyber Risk Calculator bridges this gap by providing a financial translation of your cyber risk profile. By converting complex technical vulnerabilities into clear dollar figures, it creates a common language that everyone in your organization can understand—from the server room to the boardroom.
The calculator delivers a snapshot of potential financial losses your organization could face due to a cyber incident and helps determine if you have enough in capital reserves to withstand a significant loss event. This financial clarity enables smarter decision-making on risk investments versus risk tolerance, ultimately aligning technical, financial, and operations staff around the common goal of reducing organizational risk.
What is the Cyber Risk Calculator?
The Cyber Risk Calculator delivers immediate value through a simple, low-effort process. After answering just six straightforward questions about your organization, you’ll receive a snapshot of your cyber risk exposure.
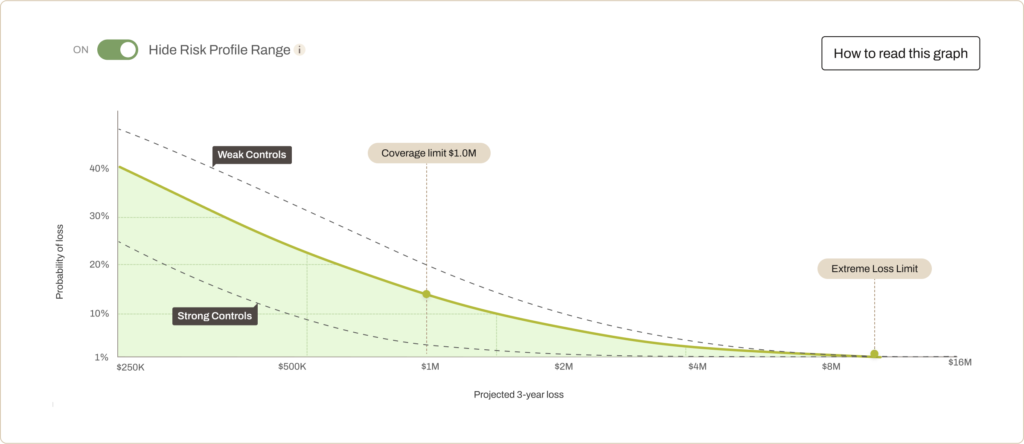
First, you’ll get a high-level estimate of your potential cyber risk using our Loss Exceedance Curve. This powerful visualization tool shows the probability distribution of loss scenarios, from frequent minor incidents to rare but catastrophic events. It provides a tangible baseline for understanding your organization’s financial exposure to cyber threats, turning abstract risks into concrete insights.
Next, the calculator generates a personalized cyber risk projection based on proprietary industry benchmarks. Unlike generic assessments, this projection is tailored to your specific industry and organizational profile, offering more relevant and meaningful insights.
Finally, you’ll see a quick comparison of your current risk exposure against your risk tolerance. This helps you evaluate whether your security posture and insurance coverage align with your organization’s risk appetite. With this financial perspective, CISOs, risk managers, and CFOs–in consultation with their insurance broker–can have more strategic, data-driven conversations about cybersecurity investments and risk transfer strategies.
How does the Cyber Risk Calculator work?
The Cyber Risk Calculator leverages a data-lite version of Resilience’s comprehensive Edge Platform risk model. It creates projections based on six key firmographic data points:
- Industry
- Annual revenue
- Number of employees
- Number of financial records
- Number of PII/HI records
- Insurance limit
While the calculator uses only 11% of the data signals leveraged by the full Edge Platform and relies on averaged security control benchmarks for similar organizations, it still provides valuable insights that can guide your risk management strategy.
Wondering how much your organization stands to lose from a cyber incident? Take the first step toward understanding your cyber risk in financial terms. Try the free Cyber Risk Calculator today.
The path to effective cyber risk management begins with understanding. Resilience’s free Cyber Risk Calculator offers a valuable first step in that journey, empowering you to have more informed conversations about risk management and make strategic decisions to protect your enterprise.
Disclaimer: Projections from the Cyber Risk Calculator are for informational purposes only. The snapshot should not be considered an exhaustive or fully accurate estimation of your risk. It does not constitute insurance advice. To determine the appropriate insurance coverage for your organization, please consult your broker.