WHY RESILIENCE?
See what the Resilience Solution has to offer
Make data-backed, informed decisions
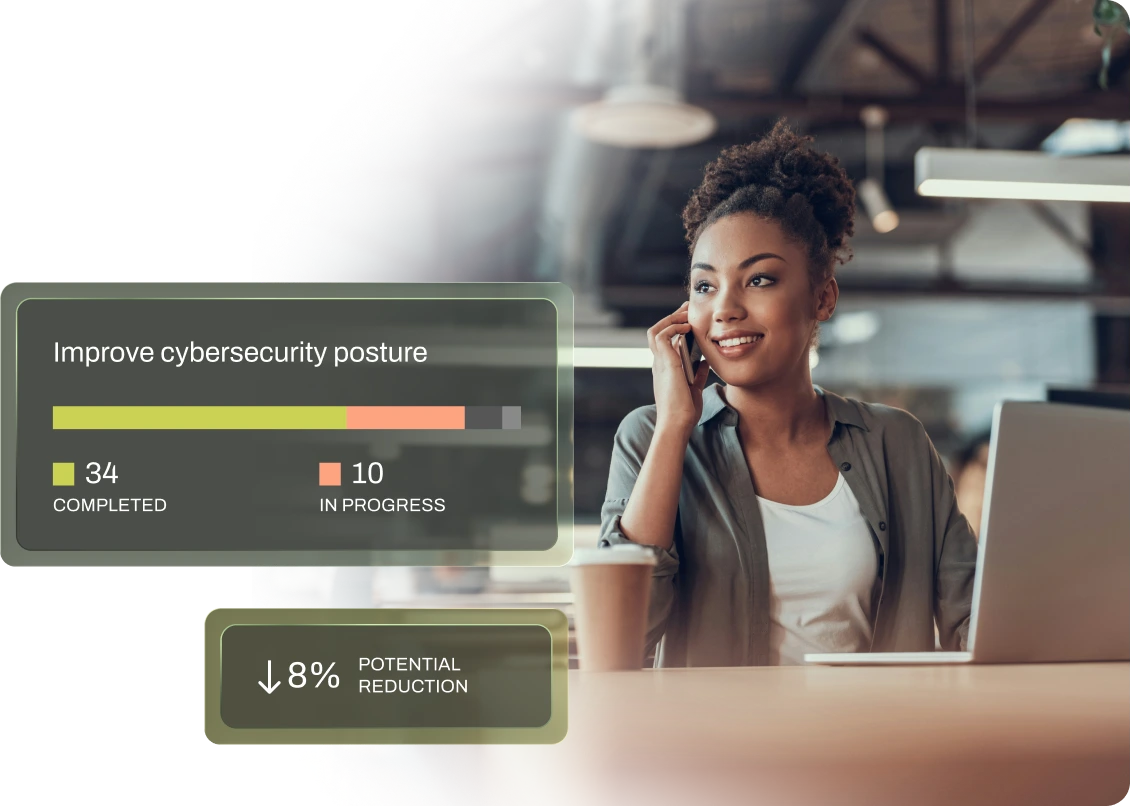
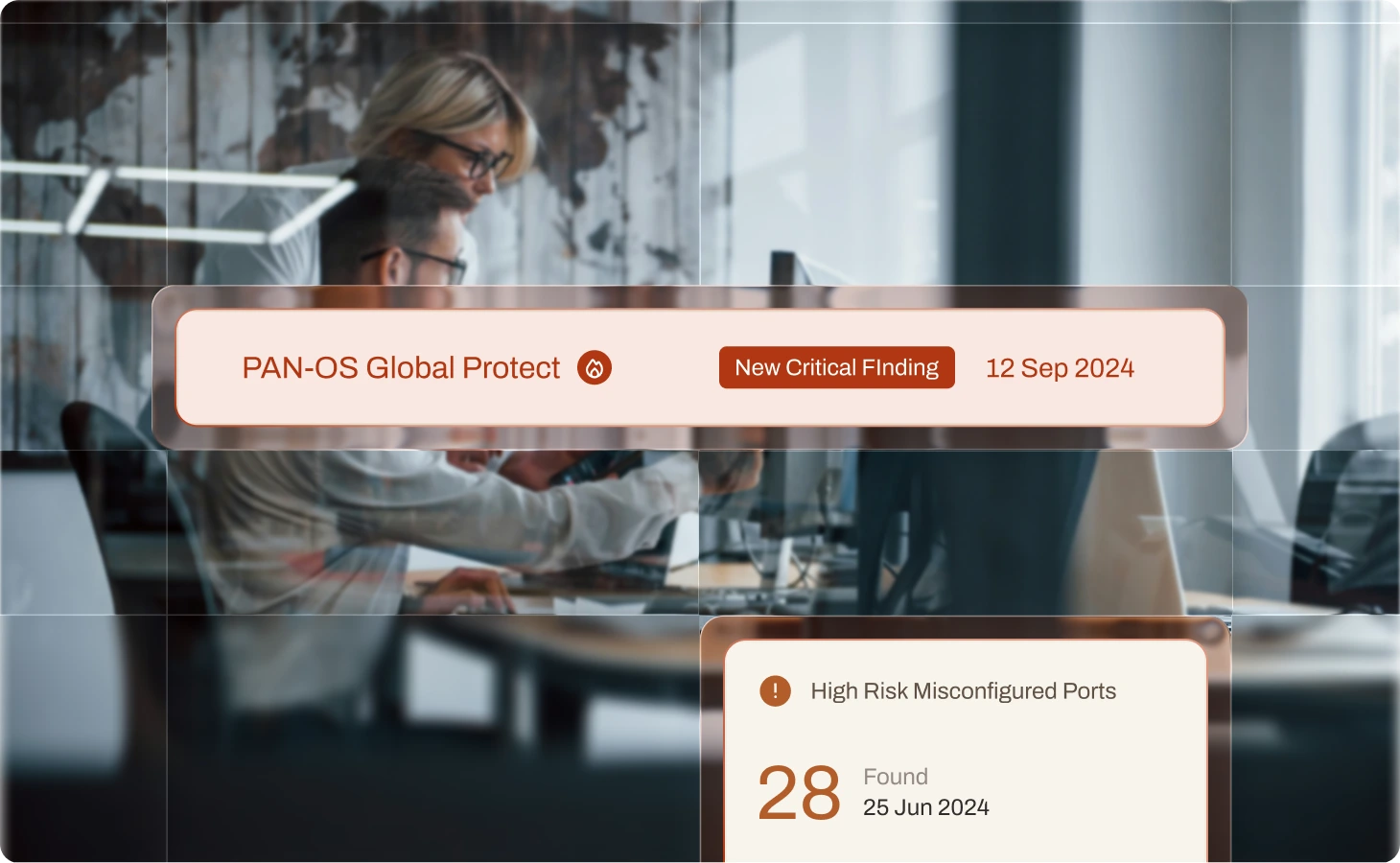
CYBER ACTION PLAN
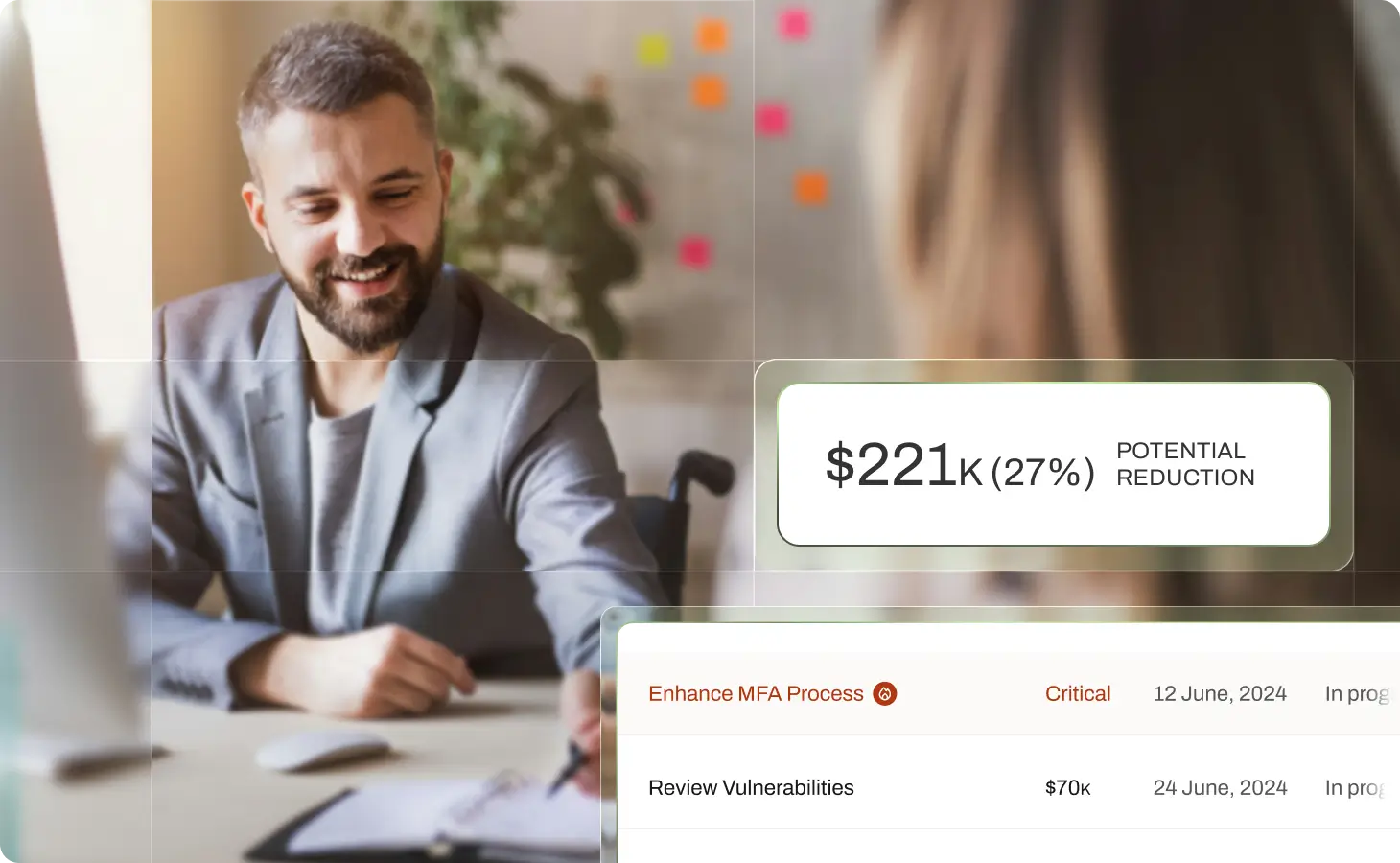
Stop wasting budget on controls that don’t actually work. We help you manage cyber risk the same way we underwrite it—by analyzing proven claims data to create clear, dollar-based action plans.
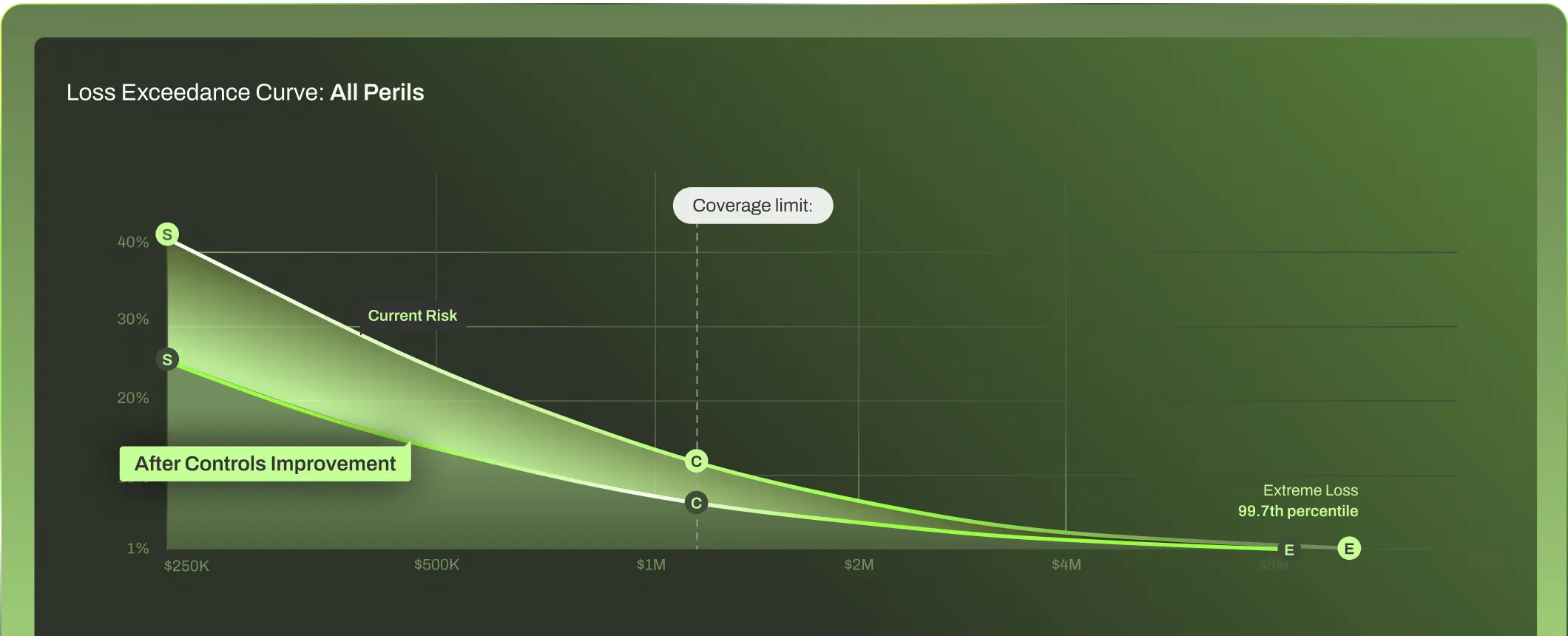
Justify and prove the value of your security program
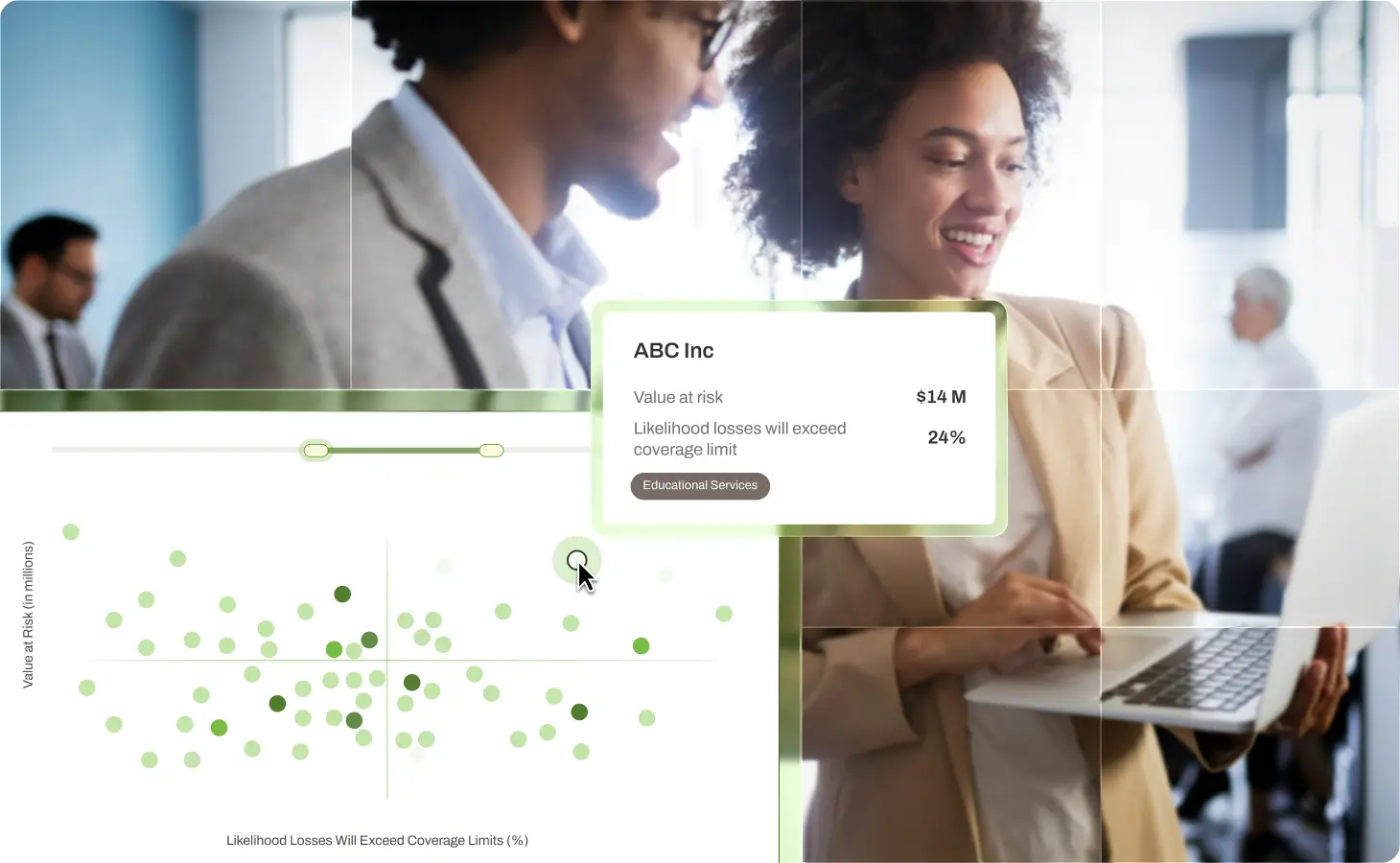
CYBER RISK QUANTIFICATION
Know which vulnerabilities can drive material loss
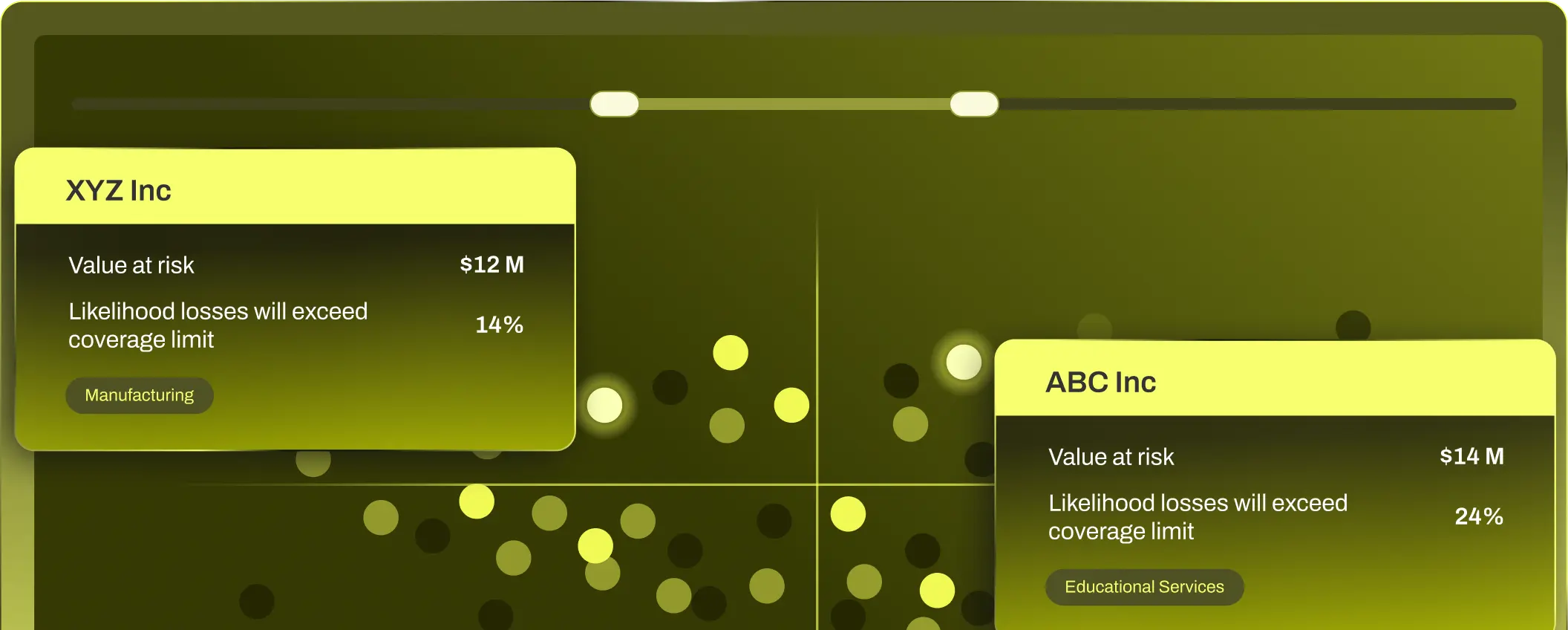
RISK OPERATIONS CENTER
Create ongoing visibility into your entire portfolio
MULTI-ENTITY & PORTFOLIO RISK
BROAD MARKET APPETITE
A global partner you can count on
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals
Available Coverage
Cyber Insurance, Tech E&O
Industries Covered
Healthcare, Higher Education, Financial Institutions & Financial Services, Manufacturing, Construction, Law Firms, Professional Services, Public Entities, Retail, Hospitality, Technology, Life Sciences, Medical Devices, Pharmaceuticals

REPORT
2025 Cyber Risk Report Shows the Impact of Cyber Resilience
Get the latest trends and analysis in cyber claims with our 2025 Cyber Risk Report and see how we’re helping organizations build Cyber Resilience.
RESOURCE CENTER
Stay ahead of cyber risk with the latest intel and insights
The time for
Resilience is now