THREATONOMICS RISK GRAPH
Accelerate cyber business decisions with AI-powered quantification
The Threatonomics Risk Graph combines security, financial, and insurance data to give CISOs and Risk Managers the business context they need to make informed cybersecurity investment decisions.
RISK-INFORMED DECISION MAKING
Every cyber decision starts with asking the right questions
What is my security posture?
By analyzing your security controls and policies, Threatonomics Risk Graph establishes a baseline of possible scenarios that could lead to loss, not a generic checklist of compliance gaps.
Where am I most exposed?
Our models pinpoint the specific vulnerabilities, attack paths, and control gaps that actually drive financial loss so you can focus your attention on where it matters most.
What is the business impact?
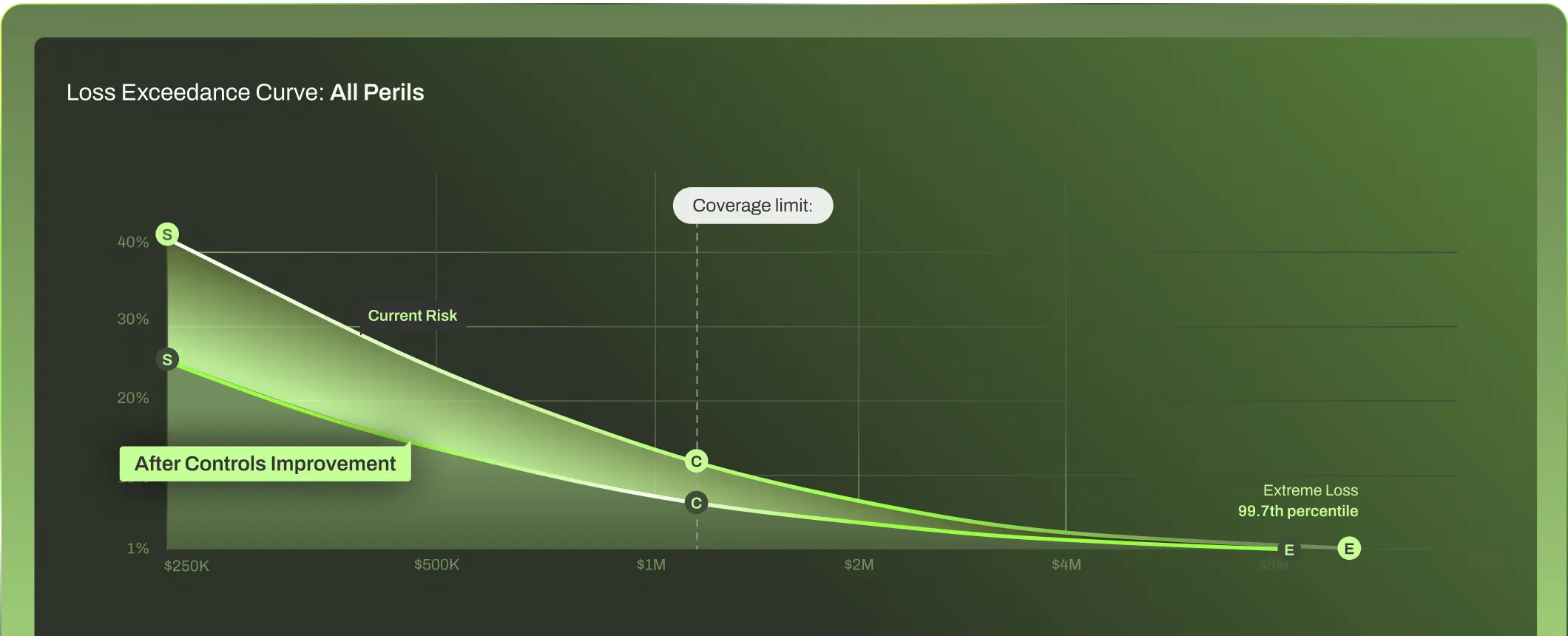
By connecting your technical exposure with financial and insurance data, our models quantify the real financial and operational severity of a cyber event.
What should I fix first for maximum impact?
The model stack-ranks the most critical actions you can take to reduce risk the fastest and deliver the greatest return on investment.
HOW IT WORKS
Cyber Risk Quantification, Powered by AI
The Threatonomics Risk Graph unifies your security and financial data with our claims data to quantify risk scenarios, surfacing portfolio-level patterns to benchmark and strengthen you risk investment decisions.
Composing Risk
Decomposing Risk
Prioritized Remediation
Portfolio Recomposition
Prioritizing security spend is guesswork if you can’t understand business impact. By bringing together security, financial, and claims data, the Threatonomics Risk Graph gives your cyber strategy the context it’s missing.
The Threatonomics Risk Graph composes your data into total risk and then decomposing it into the types of events and triggers that could directly lead to financial.
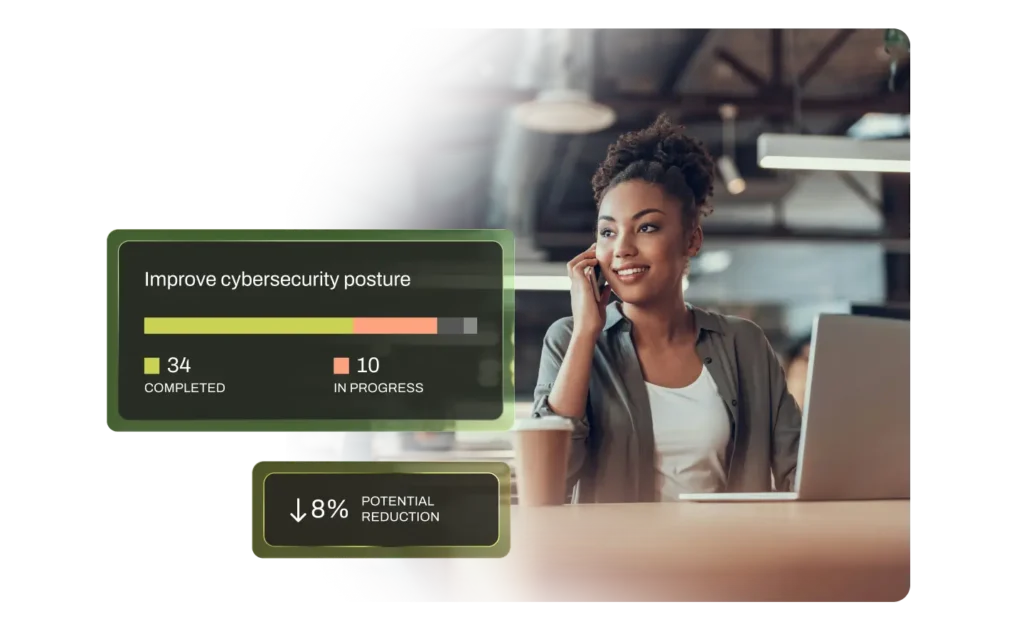
For each trigger, we list the actions your organization could take to reduce the chance of exploitation…And then prioritize those actions based on the probability and impact of financial loss, and the expected ROI of each control.
We do this for every organization, recomposing their individual risk profiles into a composite view of risk across the entire Resilience portfolio. What we learn strengthens each company we serve, fueling our collective cyber resilience.
CYBER RISK MANAGEMENT
Everything you need to measure and manage cyber risk
Cyber Insurance
Security Investment Prioritization
Multi-Entity & Portfolio Risk
Get comprehensive cyber insurance for when you need it, plus tools to prevent losses in the first place.
Top-Rated Coverage with Broad Market Appetite
Experienced, Sustainable Underwriting
24/7 in-house claims and incident management

Prioritize the risks that matter most to your business—quantified using real claims data and validated by security experts.
Real-time risk monitoring and mitigation
Financially quantified controls prioritization
Real-world attack scenario testing and validation
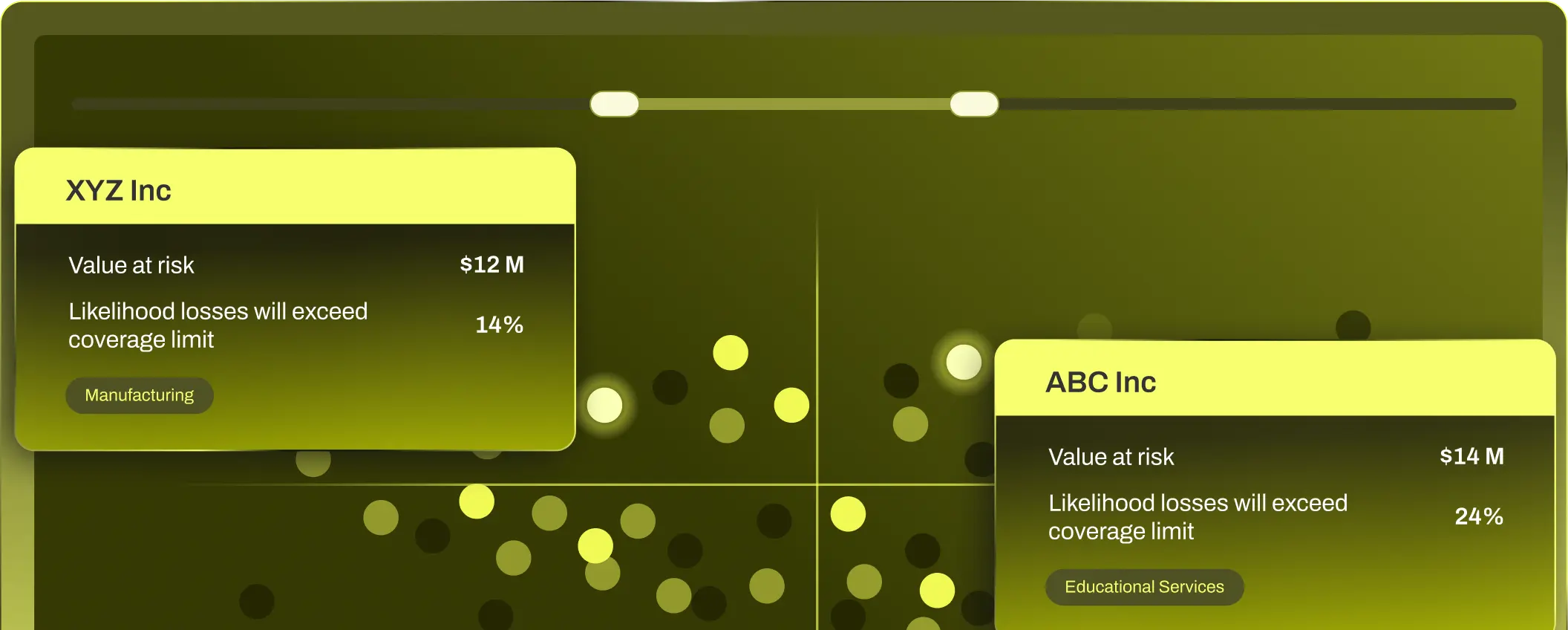
Get ongoing, dollar-based risk assessments for your entire organization—completely automated.
Automated risk assessments for every subsidiary and business unit
See which security controls matter most—ranked by dollar impact
Monitor threats across your entire organization from one place
CYBER RISK CALCULATOR
Do you know what your organization stands to lose to cyber risk?
Our cyber risk calculator measures your organization’s cyber risk, in dollar terms, to help you understand your risk exposure and potential financial losses.

OUR DATA ADVANTAGE
Only real-world financial data delivers accurate
risk quantification—in dollars & cents
Anyone can promise risk mitigation by investing more in cyber – but at what cost? Only by having access to
financial claims and loss data can you make truly informed decisions.
CUSTOMER SUCCESS STORIES
See the impact of
cyber resilience in action
Stay ahead of cyber risk with the latest threat intel and best practices
The time for
Resilience is now